⏱️ Read Time: 7 minutes
Today’s Rapid Brief is a patch-management stress test wearing a trench coat. We’ve got cPanel servers getting hammered by ransomware, Linux privilege escalation landing in CISA’s KEV catalog, security vendors dealing with source-code exposure, and AI browser extensions proving that “productivity boost” can sometimes mean “your passwords are now a group project.”
Aleph One’s “Smashing The Stack For Fun And Profit” was published in Phrack Issue 49 in 1996 and helped turn buffer overflows from niche exploit craft into required reading for generations of security engineers.📜 Table of Contents
🚨 Emerging Threats & Vulnerabilities - cPanel ransomware mass exploitation, Linux “Copy Fail” root bug, Windows Shell flaw, Mini Shai-Hulud npm campaign
🏥 Major Breaches & Incidents - Medtronic corporate IT attack, Trellix source-code repository access, Itron critical infrastructure breach
🔐 Privacy Watch - Vercel customer data theft, dental records exposure, French national ID agency hack investigation
🛰️ APTs and State Sponsored Attacks - Firestarter persistence on Cisco firewalls, China-linked covert router networks, Silk Typhoon-era extradition
🤖 AI in Cyber - AI-driven patch deadline pressure, Hugging Face LeRobot RCE, malicious AI browser extensions
🚨 Emerging Threats & Vulnerabilities
🧨 cPanel Servers Get Hit With “Sorry” Ransomware Because Apparently Web Hosting Needed More Pain
CVE-2026-41940 is being mass-exploited against WHM and cPanel servers, with attackers deploying “Sorry” ransomware across exposed systems. Shadowserver reportedly observed at least 44,000 compromised IP addresses, which is not a patching backlog, it is a five-alarm fire with a login page. Because cPanel sits at the center of website and server administration for countless organizations, this is exactly the kind of vulnerability that can turn one weak admin panel into a very expensive week.
👉️ Key takeaway: Patch cPanel and WHM immediately, validate exposed management interfaces, and assume vulnerable internet-facing servers are already being scanned.🐧 Linux “Copy Fail” Bug Gives Attackers a Path to Root, Because Root Access Was Clearly Feeling Left Out
CISA added CVE-2026-31431 to its Known Exploited Vulnerabilities catalog after evidence of active exploitation in the wild. The flaw is a Linux local privilege-escalation issue that can allow attackers to gain root access on affected systems. That makes it especially ugly in cloud, container, and shared infrastructure environments where Linux is basically the flooring, walls, and electrical system.
👉️ Key takeaway: Treat this as a high-priority Linux patch item, especially for cloud workloads, container hosts, and systems where local access could turn into full control.🪟 Windows Shell Flaw Joins the KEV Club and Brings NTLM Theft With It
CISA ordered federal agencies to patch CVE-2026-32202, a Windows Shell flaw being exploited in zero-day attacks. The vulnerability can support NTLM hash theft and lateral movement, which means attackers may use it to move from “we got one box” to “we are now touring the network.” CISA set a May 12 patch deadline for federal agencies, but private-sector teams should not treat that as a casual calendar suggestion.
👉️ Key takeaway: Prioritize remediation, monitor for NTLM-related abuse, and review lateral movement detection before attackers do your internal network mapping for you.🧬 Mini Shai-Hulud Hits npm Packages in the SAP Developer Orbit
Unit 42 says a late-April “Mini Shai-Hulud” campaign targeted four compromised npm packages tied to the SAP developer ecosystem. Those packages reportedly had roughly 570,000 combined weekly downloads, which gives this campaign a healthy supply-chain blast radius. The scary part is not just the package compromise, it is how quickly trusted developer tooling can become an attacker’s delivery service.
👉️ Key takeaway: Audit npm dependencies, pin trusted versions where possible, and watch for unusual package updates tied to SAP development workflows.
🏥 Major Breaches & Incidents
🫀 Medtronic Says Corporate IT Was Hit, But Medical Operations Stayed Online
Medtronic disclosed that a cyberattack affected its corporate IT network, but said products, patient safety, manufacturing, and distribution were not disrupted. That separation matters because medical-device makers sit deep inside healthcare supply chains, where downtime is never just an “IT issue.” Reuters also framed the incident against recent disruption at peer Stryker, making this a clean executive-risk reminder for healthcare continuity planning.
👉️ Key takeaway: Segmentation between corporate IT and operational systems is doing real work here, and healthcare suppliers should make sure theirs is more than a diagram in a slide deck.🛡️ Trellix Confirms Source-Code Repository Access, Which Is Awkward When Security Is the Product
Trellix confirmed unauthorized access to a source-code repository, while saying it found no evidence that its release or distribution process was affected. That is an important distinction, but source-code exposure at a cybersecurity vendor still raises supply-chain and trust questions. Attackers can mine exposed code for logic flaws, secrets, architectural clues, or anything else that turns “read-only” into “regret later.”
👉️ Key takeaway: Security vendors need to communicate clearly on repository access, build integrity, and whether exposed code could create downstream customer risk.⚡ Itron Discloses Cyberattack on Critical Infrastructure Tech Systems
Itron, a provider of technology for water, gas, and electricity utility systems, disclosed that hackers accessed some of its systems. The company said operations continued in all material respects, which is the phrase you use when the fire alarm is off but everyone is still staring at the ceiling. With Itron serving technology across more than 110 million homes and businesses, even a contained incident deserves attention from infrastructure and utility leaders.
👉️ Key takeaway: Critical-infrastructure vendors remain high-value targets, and customers should review vendor incident communications, access paths, and continuity dependencies.
Your next campaign brief writes itself.
Most marketing teams spend Monday morning pulling numbers. Viktor spends it posting them. Cross-platform brief in #growth before the first standup. Spend anomalies flagged before they compound.
Your marketing team stops reporting and starts deciding.
🕵️ Privacy Watch
🧾 Vercel Says More Customer Data Was Stolen Before It Spotted the Breach
Vercel said attackers accessed some customer data before the company discovered the incident. The breach was reportedly linked to compromise involving an employee’s use of Context AI, adding another entry to the growing “AI tooling created a security headache” file. For companies moving fast with developer platforms and AI assistants, this is a reminder that convenience does not automatically come with adult supervision.
👉️ Key takeaway: Review employee AI-tool usage, third-party app permissions, and data access controls before shadow productivity tools become shadow breach paths.🦷 Dental Software Bug Exposed Patient Records Through Guessable Portal URLs
A dental practice software bug reportedly allowed a patient to change document numbers in a portal URL and access other patients’ medical records. Exposed data included personal information, medical histories, and photo IDs, which is exactly the kind of privacy failure that makes “basic access control” sound less basic. The vendor says its software is used by more than 5,000 dental practices, giving the bug a wide healthcare privacy footprint.
👉️ Key takeaway: Healthcare portals need strict object-level authorization checks, not URL roulette with patient records as the prize.🪪 France Investigates 15-Year-Old Over Alleged National ID Agency Hack
French prosecutors are investigating a teenager suspected of breaching the agency that processes passports, national IDs, residence permits, and driver’s licenses. Authorities allege the suspect attempted to sell millions of citizens’ personal data, which is quite the résumé entry for someone still young enough to be grounded. The privacy stakes are obvious because identity-document systems hold the kind of data people cannot simply rotate like a password.
👉️ Key takeaway: Government identity systems need strong monitoring, segmentation, and data access controls because the attackers are not always who defenders expect.
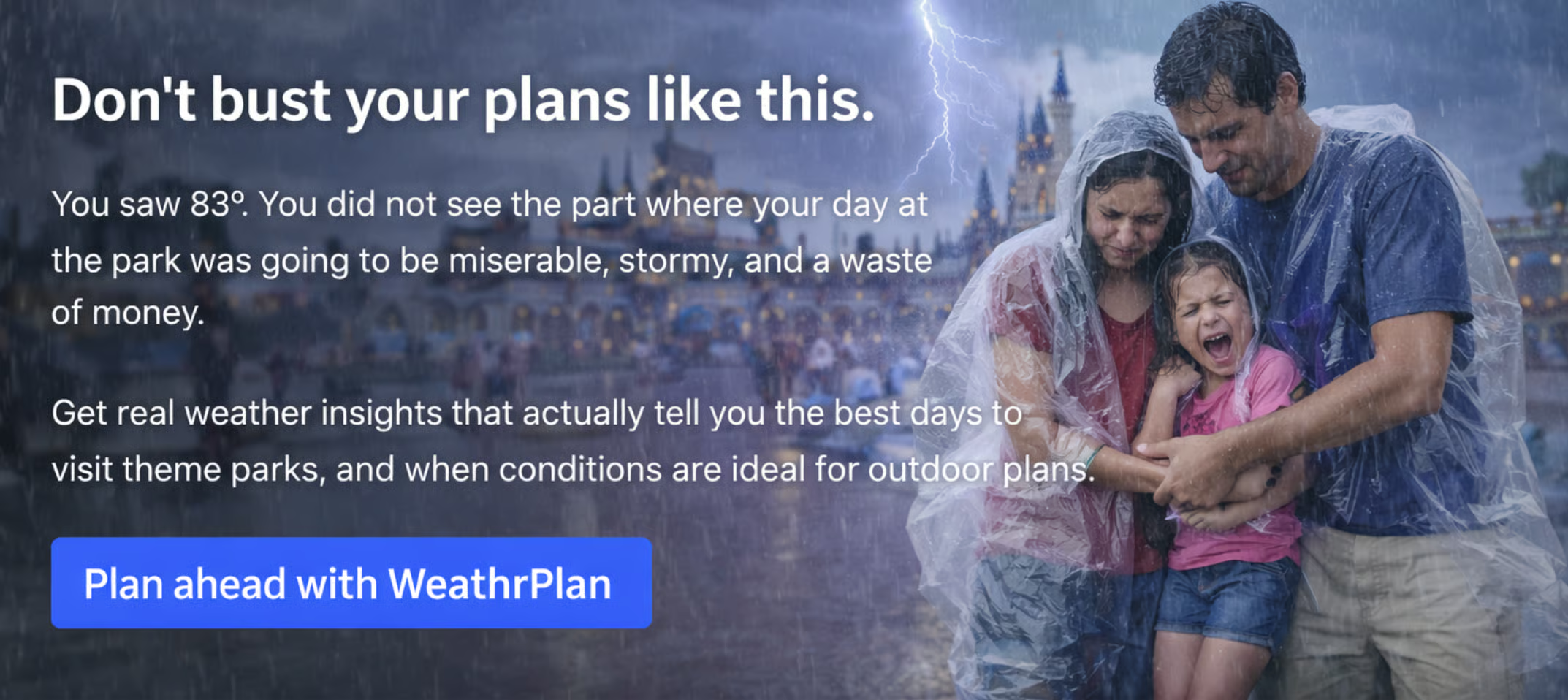
Don’t let bad weather ruin your kids’ favorite day of the year.
Most weather apps tell you the temperature.
WeathrPlan tells you whether it’s actually a good time to go.
Plan smarter with weather insights for theme parks, road trips, and vacations.
🌍 APTs and State Sponsored Attacks
🔥 Firestarter Malware Survived on Cisco Firewalls After Patches, Because Persistence Is the Point
U.S. and U.K. agencies warned that a state-sponsored group implanted Firestarter malware on Cisco network security devices. The campaign reportedly affected government and critical-infrastructure networks and had activity dating back to at least late 2025. The uncomfortable lesson is that perimeter-device compromise may survive firmware updates and reboots, so “we patched it” is not the same as “we evicted them.”
👉️ Key takeaway: For compromised network appliances, organizations need forensic validation, configuration review, credential rotation, and full persistence checks after patching.📡 China-Linked Hackers Are Building Covert Networks From Everyday Routers
Allied agencies warned that China-nexus actors are shifting toward large-scale networks of compromised everyday devices. Instead of relying only on leased or procured infrastructure, attackers can hide inside routers and other common devices that blend neatly into normal internet noise. That makes blocking, attribution, and perimeter defense harder, because the bad traffic may come from devices that look boring right up until they are not.
👉️ Key takeaway: Router hygiene, edge-device patching, default credential removal, and anomaly detection matter because “consumer-grade” does not mean “irrelevant to national cyber operations.”⚖️ Chinese National Extradited to U.S. Over Alleged Exchange Attacks Tied to Silk Typhoon Era
A Chinese national was extradited to the U.S. over alleged involvement in cyber activity linked to the Microsoft Exchange exploitation era and pandemic-related research targeting. This is less about a fresh technical exploit and more about accountability for major espionage operations that shaped enterprise security for years. It also shows that cyber cases can move slowly, but they do not always disappear into the geopolitical fog machine.
👉️ Key takeaway: Law-enforcement follow-through matters, but defenders still need to treat old campaign infrastructure, tradecraft, and exploited products as long-tail risk.
Say user_id. Get user_id.
Wispr Flow recognizes variable names, file references, and framework syntax mid-dictation. Speak your prompt, get developer-ready text for GitHub, Jira, or your editor. No mangled syntax. Ever.
🤖 AI in Cyber
⏱️ U.S. Officials Weigh Three-Day Patch Deadlines as AI Shrinks the Exploit Window
Reuters reports that CISA is considering cutting federal deadlines for actively exploited vulnerabilities from roughly two or three weeks to as little as three days. The concern is that AI-powered tools could compress the time attackers need to find, weaponize, and scale exploitation. Translation: the old patch calendar may be about to meet the new attacker stopwatch, and the stopwatch is winning.
👉️ Key takeaway: Organizations should prepare for faster patch expectations by improving asset inventory, emergency change workflows, and exploit-driven prioritization.🤖 Hugging Face LeRobot Flaw Opens the Door to Unauthenticated RCE
CVE-2026-25874 affects Hugging Face’s open-source robotics platform LeRobot and can allow unauthenticated remote code execution. The issue stems from unsafe pickle deserialization over gRPC, which is the security equivalent of accepting a mystery package and immediately plugging it into the network. Exploitation could expose credentials, model files, connected robots, and internal systems tied to AI and robotics workflows.
👉️ Key takeaway: AI and robotics infrastructure needs the same hardening, authentication, and secure serialization discipline as any production system, maybe more.🧩 Malicious AI Browser Extensions Steal Prompts, Passwords, and Session Data
Unit 42 identified 18 AI-themed browser extensions posing as productivity tools while delivering high-risk behavior. The extensions included RATs, man-in-the-middle activity, infostealers, prompt interception, and password theft. Since browser extensions sit directly between users and AI services, they are an excellent place for attackers to collect the exact information everyone swears they are not pasting into chatbots.
👉️ Key takeaway: Lock down browser extension permissions, vet AI tools before deployment, and monitor for prompt and session-data exposure.
Thanks for reading this week’s edition. Like what you see? Forward it!
Hate everything you see or have other feedback? Reply back to this email!

