⏱️ Read Time: 6 minutes
This week’s theme is simple: trust is expensive. Third-party vendors, telecom infrastructure, legacy devices, and “secure by default” assumptions all took a hit. If your risk model still starts at the firewall and ends at the password reset button, we need to talk.
In 2017, researchers found that a casino’s high-roller database was breached through an internet-connected fish tank thermometer.📜 Table of Contents
🚨 Major Breaches & Incidents - Vercel vendor breach, ADT customer data theft, France identity agency exposure
🛠️ Emerging Threats & Vulnerabilities - Bitwarden package attack, Defender zero-day abuse, BRIDGE device flaws
🕵️ Privacy Watch - Telecom location spying, Canada SMS blaster arrests
🎯 APTs & State Sponsored Attacks - Cisco persistence breach, GopherWhisper ops, Venezuela wiper attacks
🤖 AI in Cyber - LMDeploy exploited in hours, autonomous AI cloud attacks
🔁 Story Follow-Ups - CISA KEV adds eight flaws, Dutch warning on China parity
💥 Major Breaches & Incidents
☁️ Vercel Breached Through AI Vendor Access
Vercel said attackers gained access through Context.ai, a third-party AI tool tied to an employee account. The intrusion reached portions of Vercel environments and exposed some non-sensitive environment variables. Customers were advised to rotate credentials, which usually means “this may be bigger than a routine notice.”
👉 Key takeaway: Your environment is only as secure as the least-reviewed SaaS tool with OAuth permissions.🏠 ADT Says Customer Data Stolen in Cyber Intrusion
ADT confirmed attackers stole data tied to customers and prospective customers, including names, phone numbers, addresses, birth dates, and partial SSNs or tax IDs. Payment data and monitored security systems were reportedly untouched. ShinyHunters has been linked to the incident, adding a familiar extortion flavor.
👉 Key takeaway: Security brands are still prime targets because trust itself is valuable loot.🪪 French Identity Agency Attack May Have Exposed Personal Data
France’s ANTS agency, which handles passports, IDs, residence permits, and driver’s licenses, suffered a cyberattack that may have exposed sensitive citizen data. Potentially impacted records include credentials, names, emails, birth dates, and account identifiers. That is a rough list to see next to the words “identity agency.”
👉 Key takeaway: Public-sector identity systems remain high-value targets with outsized downstream fraud risk.
🛠️ Emerging Threats & Vulnerabilities
📦 Bitwarden NPM Package Hit in Supply Chain Attack
A compromised Bitwarden CLI NPM package reportedly included malware designed to steal secrets from AWS, Azure, GitHub, GCP, SSH configs, shell history, and even AI tooling files. Bitwarden said there is no evidence vault data or production systems were compromised. Still, poisoned packages remain the attacker gift that keeps giving.
👉 Key takeaway: Verify packages, pin dependencies, and stop assuming popular brands equal safe builds.🛡️ Microsoft Defender Flaw Exploited as Zero-Day
Huntress warned CVE-2026-33825 was exploited in the wild using public proof-of-concept code. Attackers with low privileges could access the SAM database, dump NT hashes, and escalate to SYSTEM. Nothing says “defense in depth” like abusing the defense tool.
👉 Key takeaway: Security software needs the same urgent patching cadence as everything else.🔌 22 BRIDGE Flaws Expose Thousands of Serial-to-IP Devices
Researchers uncovered 22 vulnerabilities in Lantronix and Silex serial-to-IP converters, with nearly 20,000 internet-exposed devices identified. Risks include RCE, auth bypass, firmware tampering, and device takeover. Legacy infrastructure quietly connected to the internet continues to be a cursed genre.
👉 Key takeaway: If it bridges old tech to new networks, it probably deserves an immediate review.
Gladly Connect Live '26. May 4–6 in Atlanta.
The room you want to be in. This is where CX leaders are tackling the hard AI questions and sharing what's actually working. For CX and ecommerce leaders. Atlanta, May 4–6. Space is limited — secure your spot now.
🕵️ Privacy Watch
📍 Surveillance Firms Exploiting Telecom Systems for Location Tracking
Citizen Lab researchers found surveillance vendors abusing telecom systems to locate targets using hidden SMS commands and weaknesses in SS7 and Diameter protocols. These issues span both older and newer mobile networks. Old telecom flaws apparently age like mold.
👉 Key takeaway: Telecom metadata remains dangerously accessible in the wrong hands.📲 Toronto Police Arrest Three in Canada’s First SMS Blaster Case
Authorities say suspects used fake cell towers to blast phishing texts and caused more than 13 million network disruptions. This goes beyond normal smishing by impersonating carrier infrastructure itself. Criminal innovation remains unfortunately well funded.
👉 Key takeaway: Smishing is evolving from scam messages into telecom-layer attacks.
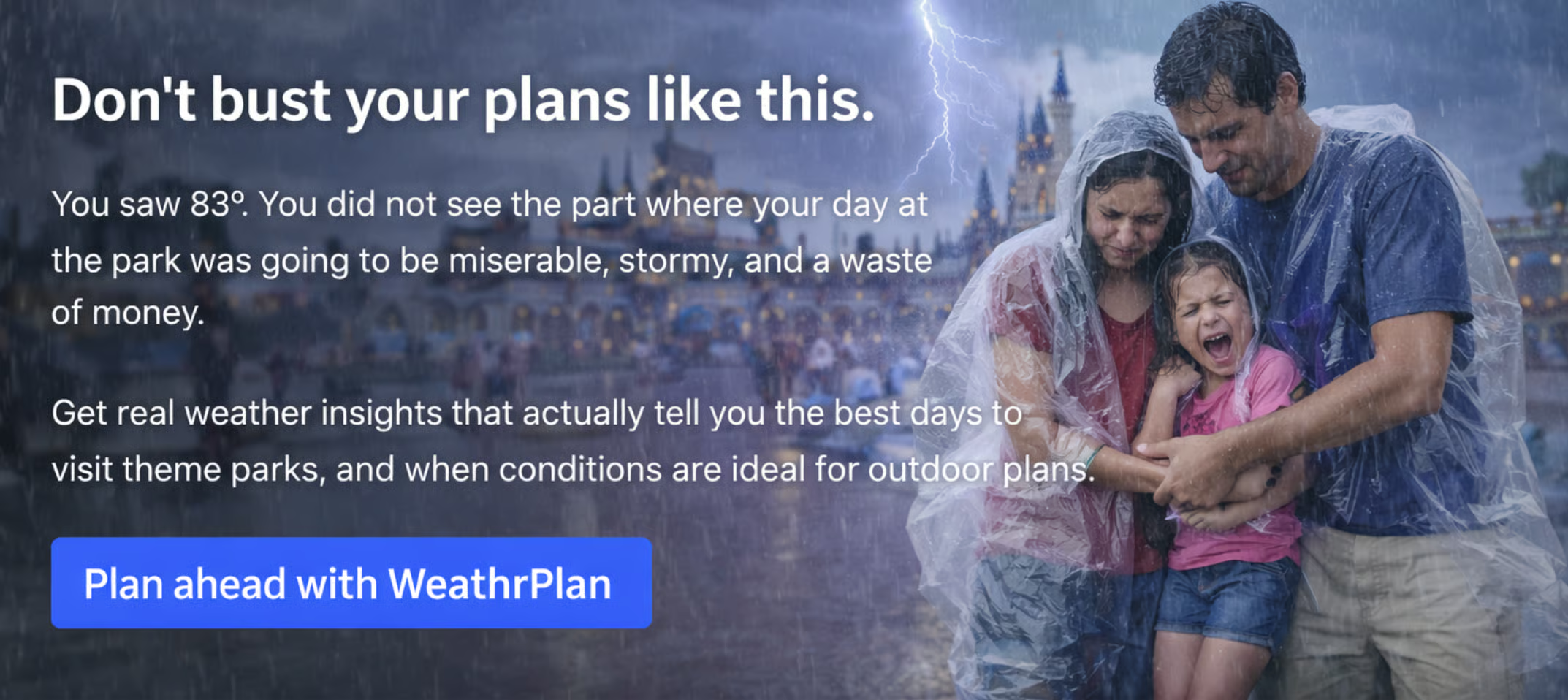
Don’t let bad weather ruin your kids’ favorite day of the year.
Most weather apps tell you the temperature.
WeathrPlan tells you whether it’s actually a good time to go.
Plan smarter with weather insights for theme parks, road trips, and vacations.
🌍 APTs and State Sponsored Attacks
🔥 CISA Warns Cisco Breach Included FIRESTARTER Persistence
CISA said a U.S. federal agency was breached through Cisco firewall flaws, with FIRESTARTER malware enabling continued access through March. That means patching the original bug may not have been enough. Persistence beats headlines every time.
👉 Key takeaway: After patching edge devices, hunt for backdoors or expect repeat visits.🛰️ China-Linked GopherWhisper Used Slack and Discord in Government Ops
ESET detailed a China-linked campaign using Slack, Discord, file.io, Microsoft Graph, and custom malware against a Mongolian government target. Using legitimate services helps blend malicious traffic into everyday business noise.
👉 Key takeaway: If your detections rely on blocklists alone, attackers already know.⚡ Wiper Malware Hits Venezuela Energy Sector
Kaspersky reported previously unknown Lotus Wiper malware used in destructive attacks against Venezuela’s energy and utilities sectors. Older Windows systems were reportedly targeted, suggesting deliberate environment selection.
👉 Key takeaway: Critical infrastructure attackers still love outdated systems with high operational value.
Wispr Flow works everywhere you type. Reply to Slack, update a Linear ticket, write a commit message — all by voice, without switching apps or breaking focus. System-level, zero setup. Start flowing free.
🤖 AI in Cyber
🤖 LMDeploy Flaw Exploited Within 13 Hours of Disclosure
A severe SSRF flaw in LMDeploy, an open-source LLM deployment toolkit, was weaponized less than 13 hours after disclosure. Successful exploitation could expose cloud metadata services and internal resources. AI tooling is now in the standard vuln-to-exploit speedrun cycle.
👉 Key takeaway: AI infrastructure now needs mature patching and exposure management, not startup optimism.☁️ Researchers Show AI Can Autonomously Hack Cloud Systems
Unit 42 tested Zealot, a multi-agent AI system that autonomously performed recon, exploitation, privilege escalation, persistence, and exfiltration in a lab environment. It was controlled research, not a real breach, but the workflow matters.
👉 Key takeaway: Agentic AI could compress attack timelines faster than many SOCs can respond.
🔁 Story Follow-Ups
📌 CISA Adds 8 Exploited Flaws to KEV
CISA added eight actively exploited vulnerabilities to the KEV catalog, including multiple Cisco Catalyst SD-WAN Manager flaws, with remediation deadlines set for federal agencies.
👉 Key takeaway: KEV remains one of the best free patch-priority feeds on the internet.🌍 Dutch Intelligence Says China Has Reached U.S. Cyber Parity
Dutch military intelligence assessed China likely now matches the U.S. in offensive cyber capability and warned many operations go undetected. Strategic warnings like this usually arrive after years of evidence.
👉 Key takeaway: Nation-state cyber competition is no longer a future trend deck topic.
Thanks for reading this week’s edition. Like what you see? Forward it!
Hate everything you see or have other feedback? Reply back to this email!
