⏱️ Read Time: 5 minutes
The term "bug" became popular in computing after engineers found a real moth trapped in a Harvard Mark II relay in 1947, which is still one of the most on-the-nose moments in tech history. Source: Computer History MuseumThis week’s brief has the full modern cyber package: critical infrastructure warnings, a large-scale government cloud mess, fresh zero-days, and AI tooling creating exactly the kind of security headaches everyone pretended would stay theoretical for at least another quarter. Cute idea. Wrong quarter.
📜 Table of Contents
🏭 Major Breaches & Incidents - Iranian hackers target critical infrastructure; Eurail breach hits 300,000; EU Commission cloud breach spreads wider
🛠️ Emerging Threats & Vulnerabilities - Windows zero-day leak; Marimo RCE under active exploitation; Adobe patches Reader zero-day
🔐 Privacy Watch - Italy fines bank $36 million over data protection failures
🕵️ APTs and State Sponsored Attacks - Feds disrupt Russia-backed espionage network; APT28 deploys PRISMEX against Ukraine and NATO allies
🤖 AI in Cyber - Mythos sparks regulatory concern; Anthropic reins in AI bug hunting; Microsoft flags better AI phishing; LiteLLM compromise hits Mercor; DeepMind maps agent attacks; GrafanaGhost exposes data leakage risk
🔁 Story Follow-Ups - Cybercrime losses hit $20.9 billion in 2025
💥 Major Breaches & Incidents
⚙️ U.S. warns Iranian hackers are shopping for exposed PLCs
U.S. agencies warned that Iranian-affiliated actors are targeting internet-exposed programmable logic controllers with disruption in mind, including possible manipulation of HMI and SCADA displays. That pushes this well beyond routine threat chatter and into high-signal operational technology risk. Water, energy, and other critical infrastructure operators should read this as the opposite of hypothetical.
👉 Key takeaway: Internet-exposed OT is still an open invitation, and adversaries are clearly reading it that way.🚆 Eurail breach turns travel data into identity-theft fuel
More than 300,000 people are being notified after Eurail said names and passport numbers were stolen in a December 2025 breach. That makes this more than a generic travel-sector incident because passport data raises the stakes fast for fraud, impersonation, and downstream abuse. Not every breach has strategic implications, but this one lands squarely in the very annoying real-world consequences category.
👉 Key takeaway: Consumer-data breaches hit differently when identity documents, not just emails and passwords, are part of the haul.☁️ European Commission cloud breach spills far beyond one inbox
CERT-EU said a breach of European Commission cloud infrastructure involved roughly 92 GB of data, including names, email addresses, and email contents, and may have affected at least 29 other EU entities. That gives this story both institutional scale and privacy impact, which is a nasty combination. When one compromise fans out across multiple public-sector bodies, governance questions arrive right behind the incident response team.
👉 Key takeaway: Cross-entity cloud breaches are a reminder that shared infrastructure can spread pain very efficiently.
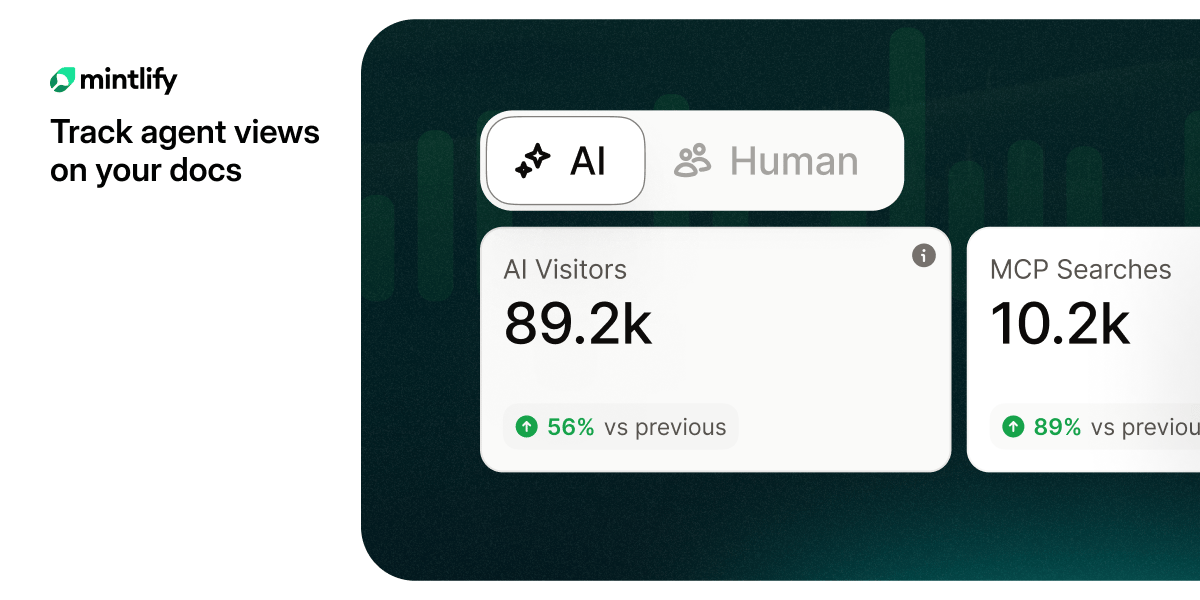
Are you tracking agent views on your docs?
AI agents already outnumber human visitors to your docs — now you can track them.
🛠️ Emerging Threats & Vulnerabilities
🪟 Leaked Windows zero-day raises the pre-patch blood pressure
A leaked Windows zero-day exploit is landing at exactly the wrong moment, right before Patch Tuesday. That timing matters because the gap between exploit visibility and patch availability is where opportunistic attackers tend to move fastest. Security teams now have the usual delightful combo of urgency, limited options, and elevated exposure.
👉 Key takeaway: Pre-patch windows are attacker playgrounds, so temporary mitigations and tighter monitoring matter right now.🧪 Marimo RCE goes from disclosure to exploitation at startup speed
Attackers began exploiting the critical Marimo pre-auth remote code execution flaw roughly 10 hours after disclosure. That is a sharp example of how little breathing room defenders get now, even when the affected software is developer tooling rather than a household enterprise platform. The weaponization timeline is getting rude enough that "we will patch soon" keeps sounding less like a plan and more like a wish.
👉 Key takeaway: Speed matters more than ever because attackers are compressing exploit timelines into hours, not days.📄 Adobe Reader zero-day gets patched after months in the wild
Adobe issued emergency fixes for a critical Acrobat and Reader zero-day that had reportedly been exploited for several months. Given Reader’s footprint across enterprise environments, this is the kind of bug that moves quickly from niche security story to universal patch priority. Long-running exploitation plus massive install base is basically the vulnerability equivalent of a fire alarm with excellent timing.
👉 Key takeaway: If Adobe Reader lives in your environment, this is a patch-now story, not a patch-when-you-get-around-to-it story.
🕵️ Privacy Watch
🏦 Italian regulator drops a $36 million lesson in internal controls
Italy’s data protection authority fined Intesa Sanpaolo after finding that an employee improperly accessed the banking information of more than 3,500 customers over a period of more than two years. The more uncomfortable part is that internal controls reportedly failed to catch it. That makes this a governance and monitoring story as much as a privacy one, which is exactly why compliance teams should care.
👉 Key takeaway: Data protection failures are not always about external attackers when weak internal oversight can do the damage just fine.
LLM traffic converts 3× better than Google search
58% of buyers now start their research in ChatGPT or Gemini, not Google. Most startups aren't showing up there yet.
The ones that are get cited by the AI tools their buyers, investors, and future hires already use. And they convert at 3×.
Download the free AEO Playbook for Startups from HubSpot and get the exact steps to start showing up. Five minutes to read.
🌍 APTs and State Sponsored Attacks
🌐 Feds shut down a Russia-backed router espionage sprawl
CyberScoop reported that Forest Blizzard, also known as APT28, compromised more than 18,000 routers across more than 120 countries using DNS hijacking and adversary-in-the-middle techniques to steal credentials and tokens. The sheer scale makes the story important. The router focus makes it worse, because network infrastructure is exactly where quiet espionage likes to live.
👉 Key takeaway: Router compromise remains a brutally effective way to turn trusted infrastructure into an espionage platform.🎯 APT28 rolls out PRISMEX against Ukraine and NATO-linked targets
Reporting tied to Trend Micro says APT28 is running a spear-phishing campaign against Ukraine and allied sectors using a new malware suite and rapid weaponization of newly disclosed flaws. That blend of geopolitical alignment and practical tradecraft is what keeps this actor relevant. It is not just persistence. It is persistence with updates.
👉 Key takeaway: State-linked campaigns keep evolving fast, which means defenders need to watch tradecraft shifts, not just actor names.
🤖 AI in Cyber
🧠 Anthropic’s Mythos model sparks regulator panic with a nicer font
Governments and regulators are scrambling to assess the risks tied to Anthropic’s latest model, Mythos. The urgency appears especially strong in financial oversight circles, which tells you this is no longer just a lab-safety or policy-debate story. Once regulators start moving this fast, the conversation has officially become operational, legal, and board-level.
👉 Key takeaway: Advanced model risk is now governance risk, and leadership teams need to treat it that way.🔍 Anthropic pulls back its AI bug hunter after it found too much
Anthropic reportedly restricted a vulnerability-hunting AI after it surfaced widespread flaws, which is both impressive and deeply awkward. The story shows how quickly capability can run into containment problems when systems become genuinely useful for cyber discovery. It is the cleanest example this week of AI power colliding with AI control.
👉 Key takeaway: As AI gets better at finding vulnerabilities, guardrails will matter just as much as raw model capability.🎣 Microsoft says AI phishing is getting sharper, faster, and more annoying
Microsoft is warning that AI-assisted phishing campaigns are growing more sophisticated, which should surprise exactly no one paying attention. The important part is not the novelty. It is the scale, speed, and improved personalization that make social engineering harder to spot and easier to automate. Human-targeted attacks are getting an efficiency upgrade.
👉 Key takeaway: Security awareness alone is not enough when attackers can industrialize convincing phishing at scale.🔗 LiteLLM compromise turns AI dependency risk into a real company incident
Mercor said it was affected by the compromise of the open-source LiteLLM project, which moves this story out of abstract supply-chain fear and into actual business impact. That matters because the AI stack is increasingly held together by fast-moving dependencies that do not always get enterprise-grade scrutiny. Convenient ecosystems are great right up until one package starts causing executive briefings.
👉 Key takeaway: AI supply-chain risk is already producing real enterprise fallout, not just theoretical dependency drama.🕸️ DeepMind maps how the web can manipulate AI agents
Google DeepMind researchers outlined a framework for how malicious web content can manipulate autonomous agents, exfiltrate data, or steer unwanted actions. It is more research-heavy than incident-driven, but the relevance is obvious as agentic systems inch into production environments. The industry is learning, again, that giving software more autonomy also gives attackers more interesting surfaces to mess with.
👉 Key takeaway: Agent security needs to be part of product design early, before hostile web content becomes the test suite from hell.👻 GrafanaGhost shows how enterprise AI features can leak data quietly
Researchers said attackers can abuse Grafana’s AI components through indirect prompt injection to exfiltrate sensitive enterprise data without obvious user awareness. That makes this one of the more practical AI-feature abuse stories in the cycle because Grafana is not some obscure toy platform. It is a reminder that adding AI to enterprise tooling can also add a very efficient new leakage path.
👉 Key takeaway: AI-enabled product features need threat modeling now, because attackers already see them as useful exfiltration channels.

Don’t let bad weather ruin your kids’ favorite day of the year.
Most weather apps tell you the temperature.
WeathrPlan tells you whether it’s actually a good time to go.
Plan smarter with weather insights for theme parks, road trips, and vacations.
🔁 Story Follow-Ups
🏛️ AI security is getting pre-release political supervision
Reuters reports that U.S. officials and tech leaders held talks on AI cyber risks before Mythos was released. That kind of pre-release engagement suggests governance norms are hardening around powerful models, especially where national security and market stability overlap. The era of launch first and sort it out later is starting to look a little less acceptable.
👉 Key takeaway: Pre-release scrutiny for powerful AI models is quickly becoming part of the operating environment, not an exception.
Thanks for reading this week’s edition. Like what you see? Forward it!
Hate everything you see or have other feedback? Reply back to this email!