⏱️ Read Time: 7 minutes
One of the earliest antivirus tools was Reaper, a program built in the early 1970s to hunt down the Creeper worm across ARPANET. Source: Purdue University Cyber TAPThis week’s theme is simple: attackers are not waiting for your patch cycle, your identity team, or your vendor review meeting. They are moving faster, hitting familiar weak spots, and once again proving that “we use a trusted platform” is not the same thing as “we configured it correctly.”
📜 Table of Contents
📉 Major Breaches & Incidents - McGraw-Hill breach tied to Salesforce misconfiguration; Booking.com customer info accessed
⚠️ Emerging Threats & Vulnerabilities - Device-code phishing jumps 37x; Microsoft fixes exploited SharePoint zero-day; Nginx UI bug under attack; ActiveMQ flaw already exploited
🕵️ Privacy Watch - Italy greenlights Meta scraping class action; EU pushes Google data-sharing proposal
🌍 APTs and State Sponsored Attacks - APT28 targets Ukrainian prosecutors; Iranian campaign puts exposed US devices in scope; Feds disrupt GRU-linked router espionage network
🤖 AI in Cyber - Project Glasswing targets critical OSS flaws; OpenAI patches Mac app trust issue after axios fallout
🔁 Story Follow-Ups - W3LL takedown leads to arrest; Google links axios compromise to North Korea
📉 Major Breaches & Incidents
🏫 McGraw-Hill’s Salesforce Misstep Turns Into an Extortion Problem
McGraw-Hill told BleepingComputer that attackers exploited a Salesforce-hosted webpage misconfiguration and accessed a limited set of internal data. The company said the breach did not impact its Salesforce accounts, customer databases, courseware, internal systems, Social Security numbers, financial data, or student platform data. That assurance now sits awkwardly next to ShinyHunters’ claim that it holds 45 million Salesforce records tied to the company.
👉 Key takeaway: Even when a company says the exposed data is limited, a cloud misconfiguration plus an extortion claim is enough to create a serious brand and trust problem.✈️ Booking.com’s Data Access Issue Leaves Travelers Exposed to the Next Scam
Booking.com said unauthorized third parties accessed some guests’ booking information, including names, email addresses, phone numbers, and details shared with accommodations. The company said customer accounts were not breached and that the incident has been contained, but it has not said how many users were affected or whether its own systems were compromised. That leaves plenty of room for follow-on fraud concerns, especially with travel-linked data in the mix.
👉 Key takeaway: Reservation data may not be a full account takeover, but it gives attackers enough context to build very convincing phishing and impersonation lures.
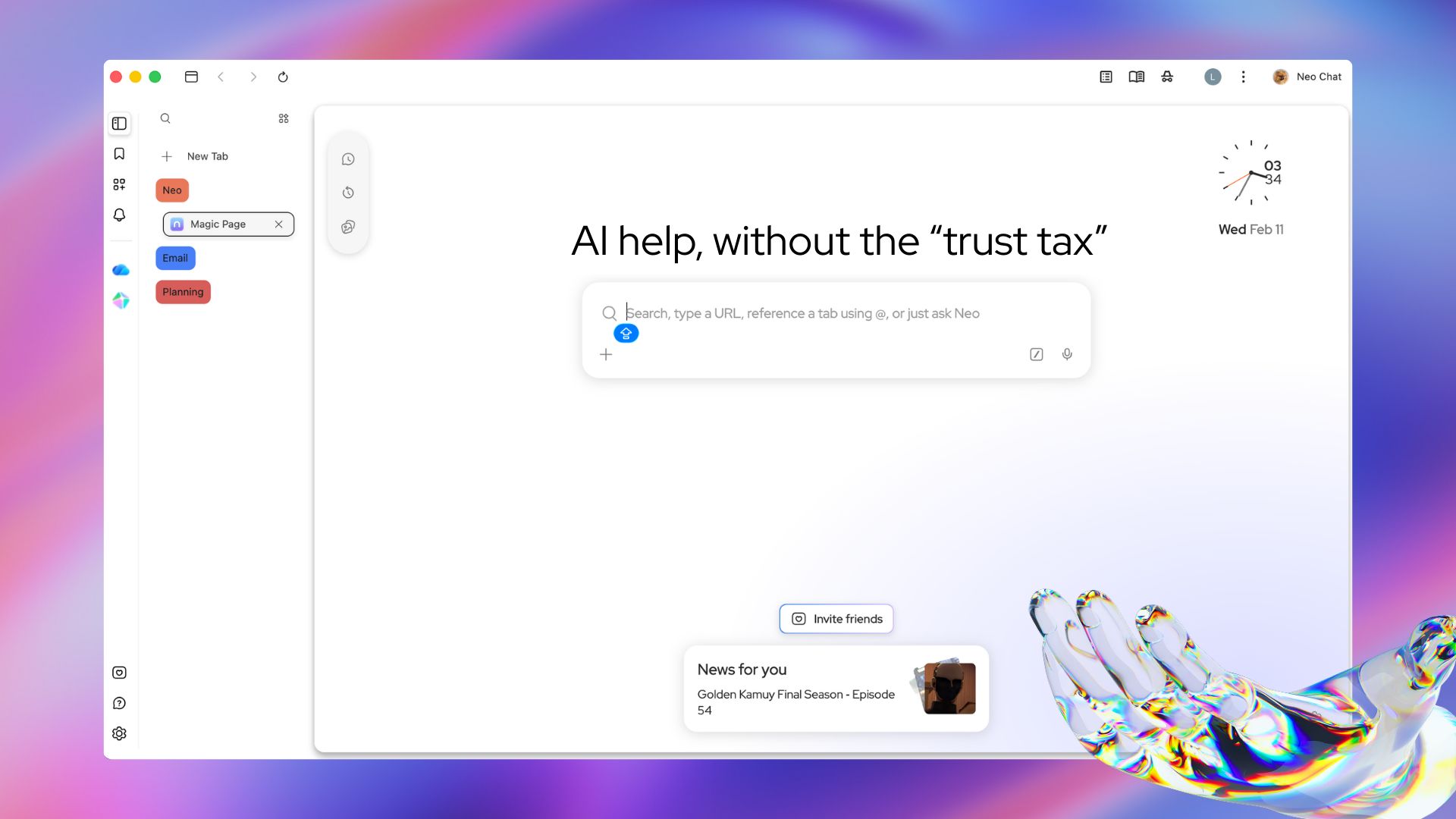
Smarter browsing. Your data never leaves the room.
Most AI tools are a trade — your data for intelligence. Norton Neo breaks that deal. Powerful built-in AI, anti-fingerprinting, VPN, and ad blocking come standard. No setup. No add-ons. No compromises. Search, summarize, and write with AI that works inside your browser and stays there.
⚠️ Emerging Threats & Vulnerabilities
🎟️ Device-Code Phishing Is Spiking Because Attackers No Longer Need Your Password
BleepingComputer reports device-code phishing attacks have surged more than 37 times this year as new phishing kits spread online. The technique abuses the OAuth 2.0 Device Authorization Grant flow, letting attackers trick users into approving a login and handing over valid access tokens instead of passwords. That makes it especially effective against Microsoft 365 and other SSO-connected services where a stolen token can do plenty of damage on its own.
👉 Key takeaway: Identity defense can no longer focus only on passwords because attackers are getting what they want without stealing them.🧩 SharePoint’s Latest Zero-Day Just Became Everyone’s Patch Emergency
Microsoft patched CVE-2026-32201, an exploited SharePoint vulnerability, in its April security release. SecurityWeek reported that Microsoft described the bug as an improper input validation issue that could let an unauthorized attacker spoof over a network, access sensitive information, and alter it. CISA has already added it to the KEV catalog and ordered federal agencies to patch by April 28.
👉 Key takeaway: An exploited SharePoint flaw with a KEV deadline is not background patch noise. It is a near-term operational priority.🖥️ A Critical Nginx UI Flaw Is Already in the Wild
Attackers are exploiting CVE-2026-33032, a critical Nginx UI vulnerability that can lead to remote takeover. SecurityWeek noted there is not yet public detail on the attacks themselves, but the flaw was among 31 high-impact vulnerabilities Recorded Future observed being exploited in March. In practical terms, that puts exposed management panels in the danger zone right now.
👉 Key takeaway: When internet-facing admin software shows up on an in-the-wild exploitation list, patching and exposure review need to happen fast.📬 ActiveMQ’s Freshly Disclosed Flaw Is Already Drawing Fire
CVE-2026-34197 in Apache ActiveMQ Classic came to light roughly 10 days before SecurityWeek reported active exploitation. The bug affects the Jolokia API and can allow arbitrary code execution for an authenticated attacker, with researchers noting many instances still rely on well-known default credentials. CISA has added the flaw to KEV and set an April 30 deadline for federal agencies.
👉 Key takeaway: If a newly disclosed middleware flaw is already exploited and can be paired with weak defaults, the safe assumption is that patching is overdue.
🕵️ Privacy Watch
🧾 Meta’s Facebook Scraping Mess Is Back in Court
A Milan court allowed a class action to proceed against Meta over the Facebook scraping incident that exposed data tied to roughly 533 million users worldwide. The scraping itself is old news, but the court decision gives the case fresh regulatory and financial relevance. It is another reminder that privacy fallout does not end when the headlines do. Sometimes it just gets dressed up as litigation a few years later.
👉 Key takeaway: Privacy incidents can stay on the balance sheet long after they leave the news cycle.🔍 The EU Wants Google to Share Search Data, and Google Says Privacy Could Pay the Price
The European Commission proposed requiring Google to share search data with third-party search engines under the Digital Markets Act. Google pushed back, arguing the move could expose highly sensitive user queries and weaken privacy protections. That tension is what makes this story worth watching: competition policy and privacy policy are not always rowing in the same direction.
👉 Key takeaway: Forcing platform openness can create real policy trade-offs when the data in question is deeply personal.
HubSpot's ex-Head of Paid shares his 2026 playbook
Rex Gelb spent a decade building HubSpot's paid engine. Now he's showing founders exactly how to do it.
On April 27th, get the framework to structure, launch, and scale paid media that drives pipeline, not just traffic. 20 minutes. Live Q&A. Free.
🌍 APTs and State Sponsored Attacks
📧 Suspected APT28 Roundcube Attacks Hit Ukrainian Prosecutors
Ukrainian officials said a broader campaign they have tracked since 2023 appears tied to the same activity Reuters recently reported against prosecutors and investigators. The intrusions exploited Roundcube flaws that can execute malicious code when a victim simply opens an email, with no click or attachment needed. Researchers cited by Reuters linked the campaign to APT28, and Ukrainian officials said all signs point in that direction.
👉 Key takeaway: If opening an email is enough to trigger compromise, webmail patching and monitoring stop being routine hygiene and become mission-critical.⚙️ Iran-Linked Targeting Puts Thousands of US Industrial Devices in Scope
CyberScoop reported that Censys found more than 5,200 potentially exposed internet-connected devices tied to the Iranian government’s campaign, including nearly 3,900 in the United States. Many of the exposed systems were programmable logic controllers from Rockwell Automation and Allen-Bradley, putting the story squarely in critical infrastructure territory. That gives defenders something more concrete than a general warning: an actual exposure picture.
👉 Key takeaway: State-backed infrastructure threats hit differently when researchers can count the exposed devices and point to the sectors in play.📡 Feds Cut Off a Russia-Backed Espionage Network Spanning 18,000 Routers
U.S. authorities and researchers said Forest Blizzard compromised more than 18,000 routers across more than 120 countries before the operation was disrupted. The campaign hijacked network traffic to steal Microsoft account credentials and tokens, giving Russian operators a broad collection point for follow-on espionage. It is a sharp reminder that edge devices still make attractive state-sponsored launchpads.
👉 Key takeaway: Cheap, neglected routers can deliver outsized intelligence value when state actors turn them into credential-harvesting infrastructure.
🤖 AI in Cyber
🦋 Project Glasswing Puts AI on Open-Source Bug Hunting Duty
Anthropic launched Project Glasswing with partners including Amazon, Apple, Cisco, CrowdStrike, Microsoft, Palo Alto Networks, and the Linux Foundation to find flaws in critical open-source software. CyberScoop reported that the Claude Mythos Preview model has already identified thousands of previously unknown vulnerabilities in testing, including long-lived bugs in OpenBSD and FFmpeg that have now been patched. Anthropic also said it will keep the model restricted to partners and critical infrastructure groups because of misuse concerns.
👉 Key takeaway: This is the more credible version of AI-in-cyber: high-capability defensive use with tight access controls instead of open-ended hype.🍏 OpenAI Got Caught in the Axios Supply-Chain Blast Radius Too
OpenAI said it updated security certificates and is requiring macOS users to install the latest app versions after a GitHub workflow pulled and executed a malicious version of Axios. The company said it found no evidence that user data, internal systems, intellectual property, or software integrity were compromised. Even so, the incident was serious enough for OpenAI to treat the affected certificate as compromised.
👉 Key takeaway: Supply-chain hits do not need to fully compromise a company to force messy and expensive trust resets.
Become the go-to AI expert in 30 days
AI keeps coming up at work, but you still don't get it?
That's exactly why 1M+ professionals working at Google, Meta, and OpenAI read Superhuman AI daily.
Here's what you get:
Daily AI news that matters for your career - Filtered from 1000s of sources so you know what affects your industry.
Step-by-step tutorials you can use immediately - Real prompts and workflows that solve actual business problems.
New AI tools tested and reviewed - We try everything to deliver tools that drive real results.
All in just 3 minutes a day
🔁 Story Follow-Ups
🪝 The W3LL Takedown Now Includes an Arrest
The FBI and Indonesian authorities dismantled the W3LL phishing platform, seized its infrastructure, and arrested the alleged developer. BleepingComputer said the W3LL Store sold a $500 phishing kit that let criminals clone corporate login pages, steal credentials, and capture session tokens to bypass MFA. Authorities said the service enabled theft of thousands of credentials and attempts at more than $20 million in fraud.
👉 Key takeaway: The takedown matters because it hit both the storefront and the operator behind a phishing kit built for scale.🧪 Axios Supply-Chain Attack Picks Up a North Korea Link
Google linked the axios supply-chain compromise to a North Korean group, pushing the incident beyond “big package got hit” territory into clearer geopolitical attribution. That matters because axios has massive downstream reach, making the compromise more than just another ecosystem headache. It also gives defenders a sharper framework for understanding motive, targeting, and likely follow-on behavior.
👉 Key takeaway: Attribution changes how teams assess supply-chain risk, especially when a heavily used package may have been weaponized by a state-linked actor.
Thanks for reading this week’s edition. Like what you see? Forward it!
Hate everything you see or have other feedback? Reply back to this email!