⏱️ ≈ 7-minute read
Editor’s Note: This week’s edition has a little of everything: nation-state supply chain tampering, healthcare breach fallout, AI stack messes, and Meta quietly walking away from encrypted Instagram DMs because almost nobody used them. Which is certainly one way to evaluate a security feature.

📬 This Week’s Clickables
📌 Big News
North Korea poisons the JavaScript well with axios; Instagram drops encrypted DMs because convenience keeps winning🚨 Can’t Miss
Chrome rushes out a zero-day fix; CareCloud and Hims & Hers remind healthcare that third parties are still very much part of the blast radius; the European Commission confirms a cloud breach🤖 AI in Cyber
Langflow gets hit fast; Mercor gets caught in the LiteLLM fallout; Claude flaws expose risky trust paths; a compromised AI package threatens thousands of companies🧪 Strange Cyber Story
A port hacker helped smugglers move cocaine through compromised logistics systems and got seven years for the trouble
🚨 Big News
🧪 North Korea turned axios into a supply chain problem
Intro:
Nothing says modern software risk like one compromised package rippling across dependency chains at machine speed. This time the package in the crosshairs was axios, which is about as niche as oxygen in the JavaScript ecosystem.
What Happened:
Google Threat Intelligence Group reported on March 31 that a North Korea-nexus actor compromised the axios maintainer account and inserted a malicious dependency, plain-crypto-js, into axios versions 1.14.1 and 0.30.4. That dependency used a postinstall hook to run an obfuscated dropper that deployed the WAVESHAPER.V2 backdoor across Windows, macOS, and Linux. GTIG tied the activity to UNC1069 and said the malicious packages were live for roughly three hours.
Why It’s Important:
Axios is widely used across JavaScript projects, so even a short compromise window matters. In this case, the malicious releases targeted developers and downstream environments that would have pulled the package from a trusted source. That turns a maintainer-account compromise into a much broader downstream risk problem very quickly.
The Other Side:
The Google report focuses on the maintainer-account compromise and the malicious package versions, not on any deeper flaw in axios itself. The core issue here was trust in the publishing path, which is exactly why these incidents can spread so efficiently.
👉 Takeaway:
If package management is still treated as a developer convenience instead of a security boundary, this is your reminder. Your software supply chain is production infrastructure.
TL;DR
A North Korea-linked actor reportedly compromised axios releases and turned one of the web’s most common libraries into a possible entry point.
Further Reading: Google Cloud
When Pressure Rises, Here’s Where Leaders Turn
Costs rise. Clients delay. Pressure builds.
The Survival Hub gives you practical ways to respond from cutting costs to tightening operations and staying on top of revenue.
Built to help you take control when things feel uncertain.
🔐 Instagram is getting rid of end-to-end encrypted private* DMs that “very few” people used
Intro:
Meta’s latest security message seems to be that if a privacy feature is not popular enough, maybe it just does not need to exist. Instagram’s encrypted DMs are on the way out, and the reasoning is not exactly comforting.
What Happened:
The Verge reported on March 13 that Instagram will stop supporting end-to-end encrypted messages on May 8. Meta said the feature is being discontinued because “very few people” were using it, and Instagram has started notifying users to download their encrypted chats and images before removal. The company’s practical alternative is simple: use WhatsApp instead.
Why It’s Important:
This is bigger than one retired feature. It shows how fragile privacy improvements can be when they are optional, underexplained, and never made normal user behavior. Stronger protections often lose when they add friction, and that tradeoff rarely hurts platforms first. It lands on users who assume private messaging still comes with meaningful privacy defaults.
The Other Side:
Meta can argue that underused features create complexity and support burden. That is fair enough operationally, but removing privacy features instead of making them easier to use is still a very large shrug disguised as efficiency.
👉 Takeaway:
When platforms say people did not use the security feature, the better question is whether the feature was ever given a real chance to succeed.
TL;DR
Instagram is removing encrypted DMs on May 8, showing once again that convenience still beats stronger default privacy on major platforms.
Further Reading: The Verge
NIST notes that the Data Encryption Standard became the first standardized encryption algorithm in 1977. Which is a neat reminder that the fight over strong encryption is older than quite a few of today’s platforms.
🔥 Can’t Miss
🛠️ Exploited Zero-Day Among 21 Vulnerabilities Patched in Chrome
Google released a Chrome update fixing 21 vulnerabilities, including CVE-2026-5281, a use-after-free flaw in the Dawn graphics layer that was already being exploited in the wild. The patch set included 19 high-severity issues, which is not exactly a calm week for browser security.👉 Key takeaway: Patch Chrome quickly and keep treating the browser like a frontline enterprise asset, because attackers definitely do.
🏥 Health data giant CareCloud says hackers accessed patients’ medical records
CareCloud disclosed unauthorized access on March 16 to one of six environments storing patient medical and healthcare records. The company said hackers had access for more than eight hours and that it was still unclear whether data had been exfiltrated.👉 Key takeaway: In healthcare, “we’re still determining impact” is not especially soothing when protected patient data was within reach for eight hours.
💊 Telehealth giant Hims & Hers says its customer support system was hacked
Hims & Hers said hackers broke into its third-party ticketing system and stole customer support data. That matters because support platforms often hold exactly the kind of personal context attackers want for fraud, impersonation, and social engineering.👉 Key takeaway: Third-party support tooling is part of the attack surface, not a back-office footnote.
🇪🇺 European Commission confirms cyberattack after hackers claim data breach
The European Commission confirmed a cyberattack affecting cloud infrastructure tied to its Europa.eu web presence after hackers claimed they had stolen data. Officials said the incident was contained and that internal systems were not affected.👉 Key takeaway: Even when internal systems are untouched, a cloud breach at a top EU institution is still a trust and governance problem with international consequences.
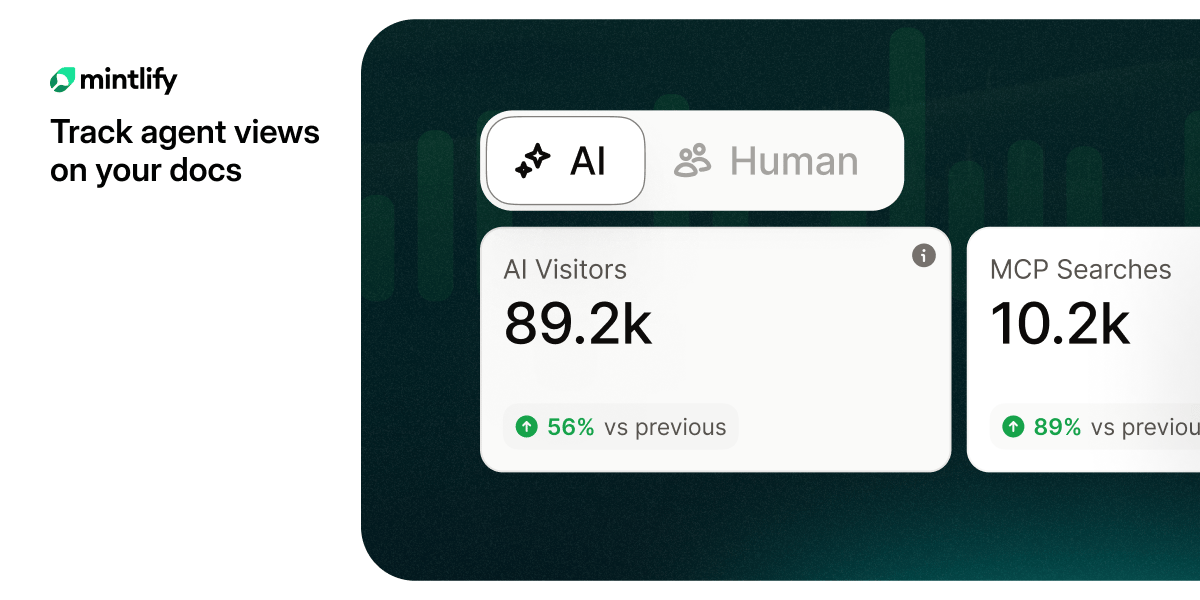
Are you tracking agent views on your docs?
AI agents already outnumber human visitors to your docs — now you can track them.
🤖 AI in Cyber
🤖 Critical Flaw in Langflow AI Platform Under Attack
Dark Reading reported that CVE-2026-33017 in Langflow was exploited in the wild shortly after disclosure and added to CISA’s Known Exploited Vulnerabilities catalog. The bug carries a 9.8 CVSS score, and researchers said exploitation attempts showed up in less than 24 hours. AI platforms are now being treated like any other high-value enterprise application, because that is exactly what they are.👉 Key takeaway: AI platforms do not get special protection just because they are new. Patch windows are shrinking there too.
💼 Mercor says it was hit by cyberattack tied to compromise of open source LiteLLM project
Mercor confirmed a security incident linked to the compromise of the open source LiteLLM project and said it was one of thousands of affected companies. TechCrunch noted it remains unclear how the stolen data was obtained or how many downstream organizations were ultimately impacted.👉 Key takeaway: In AI supply chain incidents, the technical compromise is only half the headache. The fog around downstream impact is the other half.
☁️ ‘Claudy Day’ Trio of Flaws Exposes Claude Users to Data Theft
The Claudy Day research described a three-flaw chain that could turn a Google search result into a malicious pre-filled Claude chat URL. From there, the attack could inject hidden instructions, push users to convincing fake links, and steal sensitive data. It is a useful example of how familiar web abuse now blends neatly with LLM trust failures.👉 Key takeaway: A lot of AI abuse looks less like science fiction and more like classic attack chaining with a shinier middle layer.
📦 Supply chain attack hits widely-used AI package, risks impacting thousands of companies
The Record reported that LiteLLM was compromised in a supply chain attack that researchers said could impact tens of thousands of environments. The affected versions were live on PyPI for at least two hours, and Sonatype said the package sees roughly three million daily downloads. This is the nightmare version of fast AI adoption: one shared component and a very long downstream review list.👉 Key takeaway: If an AI package sits deep enough in the stack, compromising it can turn one repo problem into an enterprise-wide incident.
Don’t let bad weather ruin your kids’ favorite day of the year.
Most weather apps tell you the temperature.
WeathrPlan tells you whether it’s actually a good time to go.
Plan smarter with weather insights for theme parks, road trips, and vacations.
🧟♂️ Strange Cyber
🚢 A hacker used port systems to help smuggle cocaine. The court was not impressed.
Intro:
Cybercrime occasionally crashes into the physical world in ways that feel almost too on-the-nose to be real. This one involved hacked port systems, container logistics, and organized crime deciding digital access was just another useful shipping tool.
What Happened:
The Record reported in January that a Dutch appeals court sentenced a 44-year-old man to seven years in prison for hacking a major port company in Belgium to help smuggle cocaine into the Netherlands. Prosecutors said the operation enabled the import of 210 kilograms of cocaine through Rotterdam, and court records said the defendant convinced a port employee in Antwerp to insert a USB stick loaded with malware into a work computer. That created a backdoor into systems used to manage containers and access controls.
Why It’s Important:
Port systems are not just databases and dashboards. They influence trade flows, customs workflows, cargo movement, and, apparently, criminal logistics for people who appreciate efficiency. It is a good reminder that cyber compromise does not stop at data theft when the target sits inside real-world infrastructure.
The Other Side:
Yes, this story is older than the rest of the edition. It still earns the slot because the lesson holds up perfectly well: logistics environments attract not just nation-states and ransomware crews, but also organized crime groups that know access can move more than information.
👉 Takeaway:
If cyber access can reroute containers, it can reroute far more than data. Digital compromise in logistics is a real-world force multiplier.
TL;DR
A Dutch court sentenced a hacker to seven years for using port system access to help smuggle cocaine, proving once again that cybercrime loves an efficient supply chain.
Further Reading: The Record
Enjoying Exzec Cyber? Forward this to one person who cares about staying ahead of attacks
Hate everything you see or have other feedback? Reply back to this email!