⏱️ ≈ 7-minute read
Editor’s Note: This week’s lineup checks several cyber bingo boxes: government surveillance infrastructure getting breached, zero-day exploitation hitting new highs, and attackers continuing to turn random devices into launchpads for ransomware. If there’s a theme this week, it’s this: attackers keep finding weird angles into systems that defenders assumed were already covered. Also, if your threat model doesn’t include webcams yet… it might be time to update the spreadsheet.

📬 This Week’s Clickables
📌 Big News
FBI probes breach of surveillance and wiretap systems; Google tracks surge in zero-day exploitation
🚨 Can’t Miss
LexisNexis breach confirmed, Tycoon 2FA phishing platform dismantled, Qualcomm zero-day attacks, VMware Aria exploitation
🤖 AI in Cyber
AI agent framework flaws, Chrome Gemini privilege escalation, MS-Agent compromise risk, hackers weaponize AI attack tool
🧪 Strange Cyber Story
Ransomware gang bypasses EDR by launching attacks through a webcam
🚨 Big News
🕵️ FBI Investigates Breach of Surveillance and Wiretap Systems
Intro:
One of the most sensitive corners of U.S. law enforcement infrastructure may have been compromised. The FBI is now investigating a breach involving systems used for surveillance and lawful wiretaps.
What Happened:
According to reports, unknown attackers gained access to systems tied to the administration of court-authorized surveillance operations. These platforms are typically used by telecom providers and law enforcement to manage lawful interception requests. The breach reportedly exposed sensitive operational data related to surveillance activity, though the full scope is still under investigation. Authorities have not publicly attributed the intrusion or confirmed whether live interception capabilities were affected.
Why It’s Important:
Wiretap and surveillance systems are some of the most sensitive pieces of infrastructure in law enforcement. A breach here could expose investigation targets, ongoing operations, or even the technical methods used to conduct lawful monitoring. Beyond operational risks, it also raises broader concerns around oversight, security controls, and the private vendors that often run these interception platforms.
The Other Side:
Officials have emphasized that the investigation is still in its early stages. It is not yet clear whether attackers accessed active intercept data or simply administrative records. There is also no indication that surveillance capabilities themselves were disrupted.
👉 Takeaway:
If attackers can compromise the systems that manage surveillance infrastructure, it highlights a bigger issue: even the tools used to monitor criminals need serious monitoring themselves.
TL;DR:
The FBI is investigating a breach involving surveillance and wiretap management systems that could expose sensitive investigative data.
Further Reading:
BleepingComputer
World’s First Safe AI-Native Browser
AI should work for you, not the other way around. Yet most AI tools still make you do the work first—explaining context, rewriting prompts, and starting over again and again.
Norton Neo is different. It is the world’s first safe AI-native browser, built to understand what you’re doing as you browse, search, and work—so you don’t lose value to endless prompting. You can prompt Neo when you want, but you don’t have to over-explain—Neo already has the context.
Why Neo is different
Context-aware AI that reduces prompting
Privacy and security built into the browser
Configurable memory — you control what’s remembered
As AI gets more powerful, Neo is built to make it useful, trustworthy, and friction-light.
🧨 Zero-Days Surge as Commercial Spyware Vendors Drive Exploits
Intro:
Zero-day vulnerabilities are becoming less of a rare cyber weapon and more of a recurring line item in the threat landscape.
What Happened:
Google’s Threat Intelligence Group reported that 90 zero-day vulnerabilities were exploited in the wild during 2025, continuing an upward trend from previous years. A growing portion of those exploits were linked to commercial spyware vendors selling surveillance capabilities to government customers. These companies develop or acquire zero-day exploits and package them into spyware platforms used in intelligence operations.
Why It’s Important:
The commercial surveillance industry is increasingly shaping the global exploit ecosystem. Instead of isolated APT teams discovering vulnerabilities, an entire marketplace now exists where zero-days can be developed, traded, and deployed operationally. That commercialization is accelerating the speed at which new exploits appear in real-world attacks.
The Other Side:
Google also notes that improved defensive security controls may force attackers to burn zero-days faster. As platforms like mobile operating systems and browsers harden defenses, attackers may rely on more exploits simply to maintain access.
👉 Takeaway:
Zero-days are no longer rare strategic weapons. They are increasingly part of a growing commercial exploit economy.
TL;DR:
Google tracked 90 zero-days exploited in 2025, with commercial spyware vendors driving much of the activity.
Further Reading:
The Record
“There are two types of companies: those that have been hacked, and those that don’t yet know they have been hacked.” – John Chambers, former Cisco CEO🔥 Can’t Miss
🗂️ New LexisNexis Data Breach Confirmed After Hackers Leak Files
LexisNexis has confirmed a data breach after hackers leaked internal files tied to one of its data services. Early analysis suggests the compromised data could include sensitive information used by banks, insurers, and legal professionals for identity verification and risk analysis. Given LexisNexis’ role as a massive aggregator of identity and financial intelligence data, even a partial exposure could have wide downstream implications.
👉 Key takeaway: When a major data broker gets breached, the blast radius rarely stops at one company.🎣 Tycoon 2FA Goes Boom as Europol, Vendors Bust Phishing Platform
Europol and several cybersecurity companies coordinated an operation that dismantled infrastructure behind the Tycoon 2FA phishing platform. The service acted as a reverse proxy, allowing attackers to intercept credentials and session tokens in real time and bypass multi-factor authentication protections. Investigators say the kit was widely used by cybercriminal groups targeting enterprise email and cloud services.
👉 Key takeaway: MFA still matters, but attackers increasingly aim to sit directly inside the login flow.📱 Qualcomm Zero-Day Exploited in Targeted Android Attacks
Researchers uncovered a previously unknown Qualcomm vulnerability actively exploited in targeted Android attacks. The flaw affects chipset-level components responsible for key device operations, potentially allowing attackers to escalate privileges or execute malicious code. Qualcomm has released patches, but many Android devices may remain exposed until vendors distribute updates.
👉 Key takeaway: Hardware vulnerabilities move slower to patch, which makes them attractive targets for long-running attacks.🖥️ VMware Aria Operations Vulnerability Exploited in the Wild
A critical vulnerability affecting VMware Aria Operations is now being exploited in real-world attacks. Successful exploitation could allow attackers to execute code on monitoring servers that often sit deep inside enterprise infrastructure. Because the platform integrates with other management tools, compromise could give attackers valuable network visibility and lateral movement opportunities.
👉 Key takeaway: When attackers compromise monitoring tools, they gain a map of the environment defenders rely on to spot them.
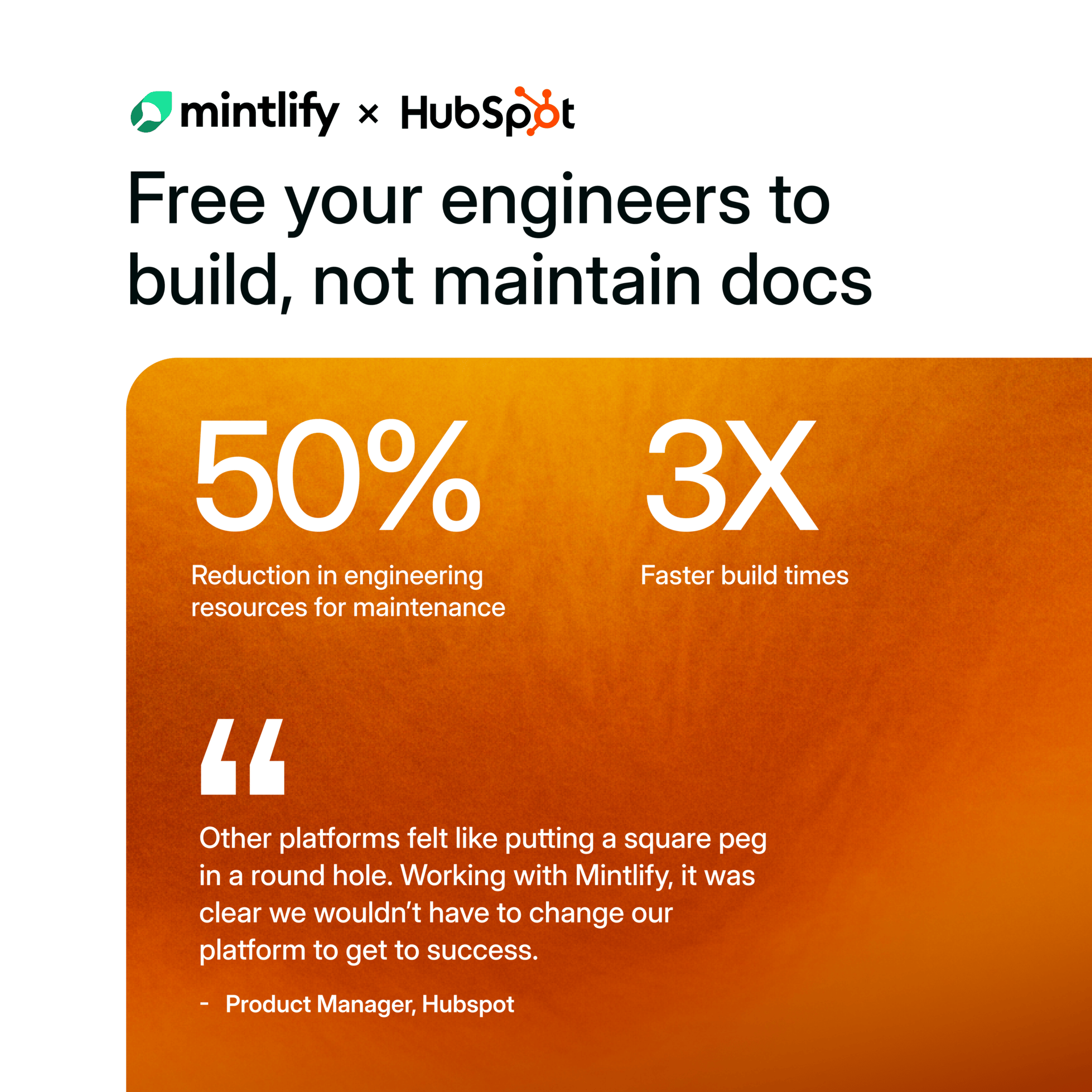
See Why HubSpot Chose Mintlify for Docs
HubSpot switched to Mintlify and saw 3x faster builds with 50% fewer eng resources. Beautiful, AI-native documentation that scales with your product — no custom infrastructure required.
🤖 AI in Cyber
🧠 Critical OpenClaw Vulnerability Exposes AI Agent Risks
Researchers discovered a critical vulnerability in OpenClaw, an AI agent framework used to automate workflows and digital tasks. The flaw could allow attackers to manipulate agent behavior or trigger unauthorized actions through malicious input or prompt manipulation. Because AI agents often operate with elevated permissions across systems, exploitation could quickly escalate into broader system access.
👉 Key takeaway: AI agents are powerful automation tools, which means their security model needs to be just as strong.🧩 Chrome Gemini Panel Vulnerability Allows Privilege Escalation
Researchers identified a vulnerability affecting Chrome extensions interacting with the Gemini AI panel. Malicious extensions could exploit how the panel communicates with browser components to gain elevated privileges. In certain scenarios, attackers could access functionality normally restricted to trusted browser processes.
👉 Key takeaway: AI features inside browsers are expanding quickly, and attackers are already probing the seams.🤖 Vulnerability in MS-Agent AI Framework Enables Full System Compromise
A vulnerability in the MS-Agent AI framework could allow attackers to fully compromise affected systems. The issue stems from how commands are passed between the AI agent and the host environment, potentially allowing arbitrary code execution. Because these frameworks are designed to automate tasks across systems, a single flaw could expose significant privileges.
👉 Key takeaway: AI orchestration tools should be treated like privileged infrastructure, not just productivity features.⚔️ CyberStrikeAI Tool Adopted by Hackers for AI-Powered Attacks
Security researchers are tracking growing adoption of a tool called CyberStrikeAI among cybercriminal groups. The platform uses generative AI models to assist with reconnaissance, automate phishing messages, and generate malware variations. By lowering the technical barrier, tools like this allow less experienced attackers to run more sophisticated campaigns.
👉 Key takeaway: AI isn’t just accelerating defenders. It’s also giving attackers a productivity upgrade.
Want to get the most out of ChatGPT?
ChatGPT is a superpower if you know how to use it correctly.
Discover how HubSpot's guide to AI can elevate both your productivity and creativity to get more things done.
Learn to automate tasks, enhance decision-making, and foster innovation with the power of AI.
🧟♂️ Strange Cyber
📷 Ransomware Gang Launches Attack Through a Webcam to Evade EDR
Intro:
Attackers are getting creative with their entry points. In this case, ransomware operators used a device that most security teams barely monitor.
What Happened:
Researchers discovered a ransomware incident where attackers leveraged a compromised webcam inside the victim network as their foothold. Because security tools were primarily focused on workstations and servers, the device slipped past endpoint monitoring. Attackers used the webcam as a staging point to move laterally across the environment before launching ransomware. The tactic effectively bypassed EDR visibility.
Why It’s Important:
IoT devices often operate quietly inside corporate networks with limited monitoring and infrequent updates. Cameras, printers, and other smart devices frequently run outdated firmware and rarely appear in threat detection dashboards. That makes them convenient hiding spots for attackers who want persistence without triggering alarms.
The Other Side:
This type of attack still requires an initial compromise of the IoT device, which may be difficult depending on network segmentation and firmware security. But once attackers get in, poorly monitored devices can provide stealthy access.
👉 Takeaway:
If it has an IP address, attackers will eventually try to use it.
TL;DR:
A ransomware gang used a compromised webcam as a stealthy foothold to bypass EDR and launch an attack across a network.
Further Reading:
BleepingComputer
Enjoying Exzec Cyber? Forward this to one person who cares about staying ahead of attacks
Hate everything you see or have other feedback? Reply back to this email!